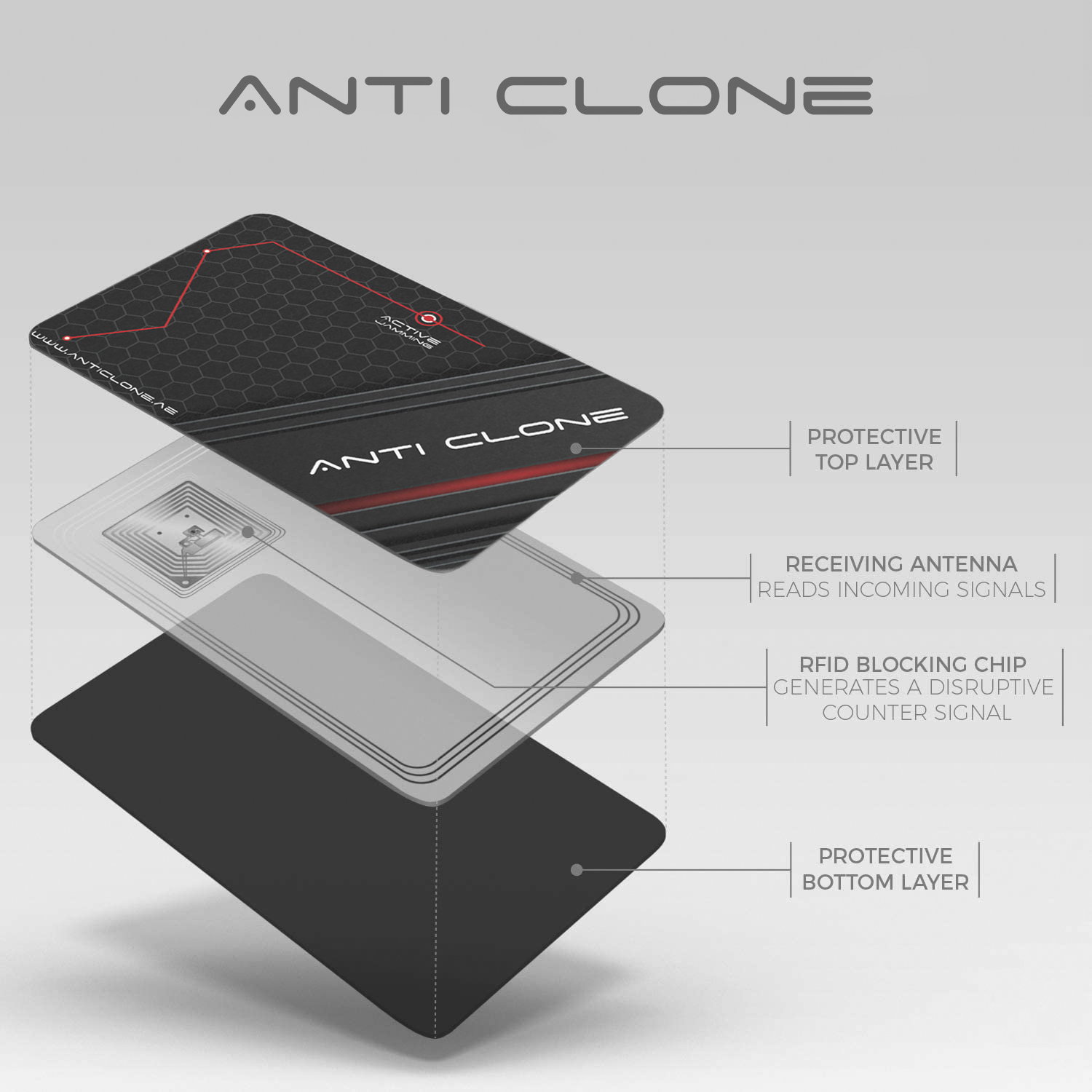
We build Anti Clone Parking Solution.
We are optimists who love to work together. Our mission is to prevent clone card access for every client, on every project. Let’s collaborate and make an impact with our cross-discipline approach to install anti clone system.